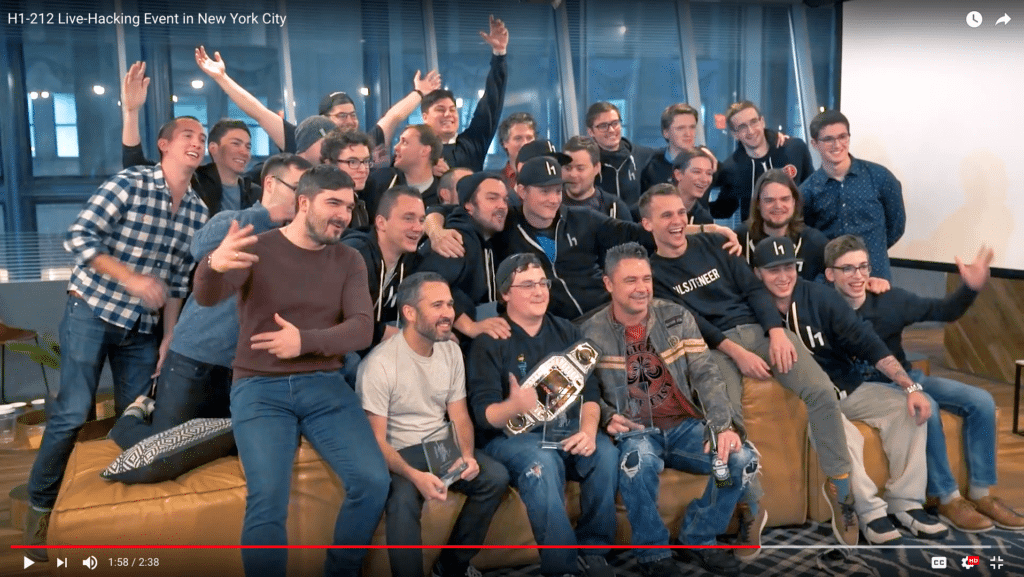
Top hackers were given awards such as “The Assassin” and “The Exalted” in addition to their bounties. (Screenshot from HackerOne promotional video)
Over the course of three weeks in December, the U.S. Air Force quietly entreated a couple dozen hackers to dig into the systems of — the U.S. Air Force.
It was the second “Hack the Air Force” event, during which trusted “white hat” hackers are brought in to help the U.S. Defense Department’s new Defense Digital Service (DDS) find flaws in its assets in exchange for cash rewards called bug bounties. Since the first “Hack the Pentagon” in May 2016, DDS has been pushing more Defense branches to get involved.
Judging by the results, it’s clear why: Hack the Air Force 2.0 revealed 106 vulnerabilities in Air Force assets, a number of them deemed critical. Since the hacker-friendly program was launched by the department less than two years ago, more than 3,000 vulnerabilities have been identified and resolved department-wide.
Some perspective might be helpful.
DDS ran a pilot with a different organization before unleashing hackers on the government. According to DDS Chief of Staff Reina Staley, the pilot event exposed 138 (since patched) vulnerabilities, costing about $150,000 in bounty money. The same asset holder had a million-dollar contract with a Washington-area cybersecurity company that had a team working on finding vulnerabilities in the same assets.
They found fewer than 20.
To run these programs, the DOD partners with HackerOne, a “hacker-powered security platform.” HackerOne sets the payout formulas for the bug bounties ahead of time, based on a number of complicated factors relating to how dangerous they are. At Hack the Air Force 2.0, the government awarded its highest single bounty so far — $12,500 — to a hacker named Brett Buerhaus who goes by the pseudonym ziot. The total payout to hackers was $103,883 over the 20-day period.
HackerOne also helps pick which prospective hackers will participate in the event. When the government started this program, it also started an amnesty-type reporting feature where hackers can safely submit bugs and vulnerabilities they have found on its platforms so that they can be corrected. From that public pool, interested hackers with good reputations and clean records might apply to participate in the official hack.
That’s where HackerOne comes in. The company does the same thing for a number of high-profile companies such as Panasonic Avionics, Google and Nintendo (though new to government, the practice of asking hackers to break your system is common in business): It vets the hackers, runs background checks if necessary and, in the case of government work, it might restrict them by nationality. That is expanding, though.
For the original Hack the Pentagon collaboration, only Americans were eligible. For the First Hack the Air Force, hackers from Five Eye countries (U.S., U.K., Canada, Australia and New Zealand) were allowed. For this latest event, participants from 16 countries cleared the screening requirements, HackerOne said.
“I never in my life thought I would be able to try and hack [the DOD] without going to jail sooner or later,” said Swedish hacker Mathias Karlsson, known in the hacking community as avlidienbrunn. Though it would have been unheard of a couple years ago, he was. And now other governments are following suit, with pilots taking place for the European Commission and Singapore Ministry of Defense as well as a number of other still-confidential entities.
You might be picturing a dark room bedecked with rows of servers, the thick, musty air tense as men alternately hunch over keyboards and argue in hushed tones, glasses reflecting the LED lights that comprise the majority of the windowless expanse’s illumination. You wouldn’t be alone in your dramatization. But you would be wrong.
Actually, the event took place in a swanky, modern co-working space in New York City with an open floorplan and lots of windows. There was a variety of mismatched tables, couches and whiteboards, and people lounged around with food while they chatted or typed away on their laptops. It was nothing like the movies.

The Air Force rented a wework coworking space in New York City to host the event. (Screenshot from HackerOne promotional video)
New compared to past government-sponsored hacks was the level of collaboration. Remediation teams were present and working with the hackers to solve vulnerabilities as they were discovered. According to Staley, most of the vulnerabilities were patched the day or week they were discovered, and ones that weren’t have been taken care of since or are still being worked on, depending on the level of involvement required to resolve the underlying issue.
That component was crucial. “It’s not just enough to know where we’re vulnerable, but it’s useless if we don’t have a mechanism to actually patch it,” Staley said. But there was a secondary benefit beyond getting a head-start on fixing bugs: it helped DOD employees to see hackers work and learn about the creative ways they would find to exploit systems.
In one example, a pair of hackers managed to pivot from a public-facing website onto a classified system on the first day. DOD personnel crowded around them, urging them on to see how far they could get, excited by the display of resourcefulness. “It was really great to see them come together in that ‘a-ha!’ moment,” Staley said.
HackerOne CTO Alex Rice repeatedly pointed to that collaboration as key in the pursuit of more secure systems.
“I think it is important to highlight that one of the inescapable truths of tech is that all software is going to have bugs and that anyone who is still acting surprised or shocked by that is just out of touch with reality,” Rice said. “And the most mature, forward-thinking, forward-leaning organizations out there are the ones that openly acknowledge that that’s not a problem that gets tackled in isolation.”

Civilian hackers and military personnel worked together to target and eliminate vulnerabilities. (Screenshot from HackerOne promotional video)
For the first part of the event, the focus was on more than 100 public-facing sites and applications, which is a much broader group of assets than past government hacks. For the second part, the team focused specifically on an application that Air Force service members use to track finances, promotions and everything from college to retirement.
“It might not sound as super sexy as hacking the F-35, but I think the implications of finding vulnerabilities in that system, in particular, are astounding,” Staley said. “If you can imagine the amount of personal and financial information that flows through this, it would be a travesty for it to be breached … It touches so many millions of lives and so many missions, any vulnerability could have a detrimental impact.”
According to Rice, that impact is one of the biggest factors motivating hackers to participate in events like this. They care what they’re working on and how big a difference they might be able to make. They might not be the type that you would expect to find in uniforms, but the repeat participants in DOD hacks in particular report a sense of patriotism as a strong motivating factor.

Surveyed hackers name a desire to test their skills and make an impact as bigger motivating factors than money in choosing what they will work on. (Screenshot from HackerOne promotional video)
Despite its growth, it has been only a year and a half since the program launched, and lessons are still being learned. DDS is still working to convince decision-makers in different branches to buy into the program. Even once they do, it takes some doing to move the money and the people around to make an event like Hack the Air Force happen.
But, as the pilot for the program indicated, the bang for the buck is outstanding. There are a number of initiatives being floated in the department to streamline the process — for instance, having a centralized pot of money from which bug bounties can be paid out — but it isn’t clear exactly what direction things will go yet. With the size of defense budgets, paying out $100,000 to get the level of troubleshooting that these events provide isn’t a concern, it’s just an issue of making sure that money is readily accessible when it’s needed.
“At least in the conversations I’ve had around the department, the money factor was never the issue,” Staley said. “It was always like ‘I’m really glad we found this; now we know our system is secure and this particular asset hasn’t been compromised and we can trust this.'”
Staley said that DDS has found its footing in a lot of ways and has a lot more of a track record to point to now when trying to get a new one of these off the ground. There are still stumbles trying to find the smoothest, most efficient way to run things, but it seems like the program can only grow going forward as it gets embraced by more branches and departments.
It goes a long way to have a higher-up on board. If someone is hesitant, it is difficult to prove value; there are vulnerabilities to point to, but those are really just things that could potentially have been misused somehow. There is no way to know if or how many catastrophes the HackerOne collaboration prevented. But Staley said this is the sort of area where it’s better to be safe than sorry.
“It’s hard to quantify the impact into a concrete number,” Staley said. “If you have a personnel system in scope where people are entering social security numbers … you can take a look at the [Office of Personnel Management] hack and the Equifax breach: it’s catastrophic and you can’t always quantify the hurt. I think it speaks for itself when we say the ‘Hey the hackers weren’t able to compromise this.'”